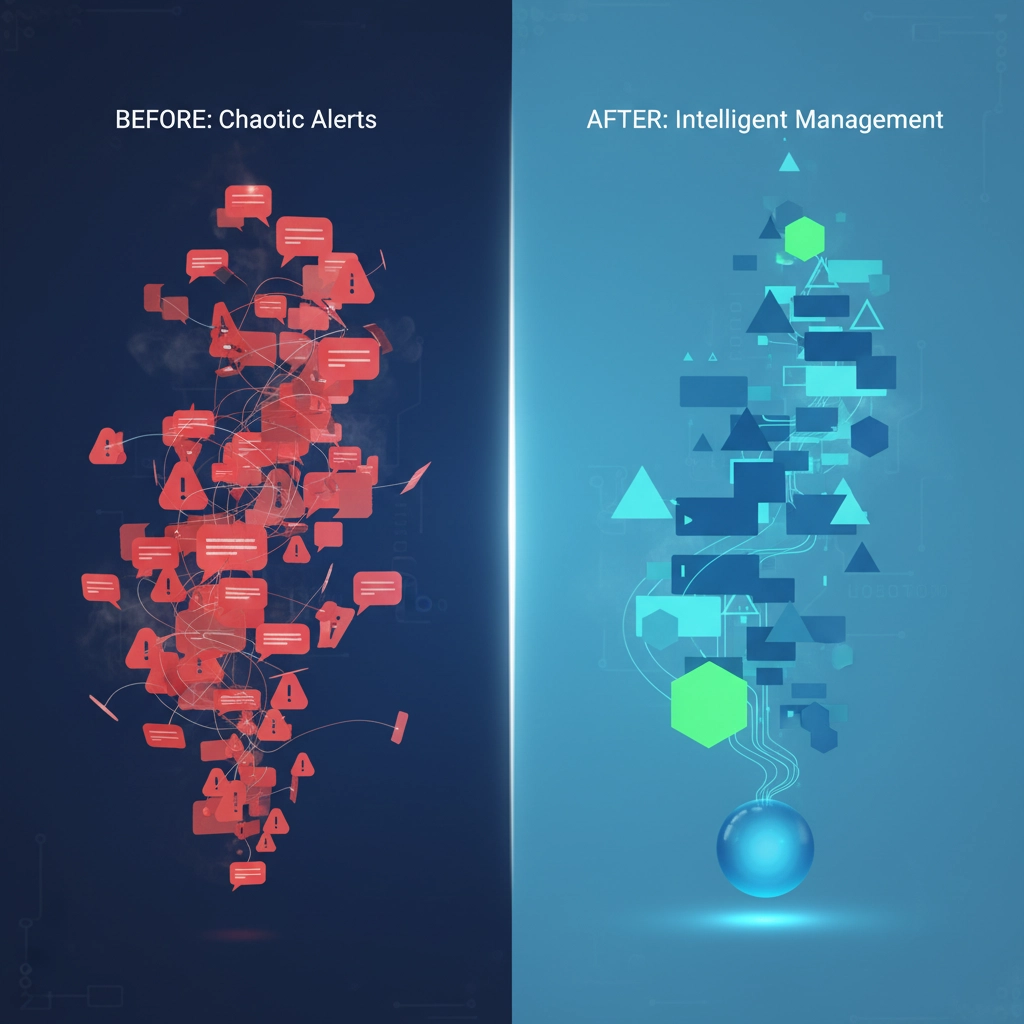
Your security team is drowning in alerts. We get it.
Between endpoint detection systems, firewalls, email security, and cloud monitoring tools, the average business receives hundreds: sometimes thousands: of security alerts every single day. The result? Alert fatigue that's making your team less effective, not more secure.
When 89% of managed service providers struggle with tool integration and 56% experience alert fatigue weekly, you're not alone in feeling overwhelmed. The good news? There are proven managed security solutions that actually reduce the noise while strengthening your defenses.
The Real Cost of Security Alert Overload
Here's what's happening in security operations centers across the country: teams spend 70% of their time investigating false positives. Critical threats get buried under routine notifications. Skilled security professionals burn out and leave for less stressful roles.
The numbers don't lie. Organizations managing 5-10 security tools report significantly higher stress levels and more missed threats than those with consolidated systems. When your team can't see the forest for the trees, real attacks slip through.

7 Managed Security Solutions That Actually Work
1. Managed Security Service Partners (MSSPs)
Think of MSSPs as your external security department that never sleeps. These partnerships consolidate multiple security functions under one roof, giving you 24/7 monitoring without the overhead of hiring and training specialized staff.
What makes this work: Instead of managing relationships with 5-10 different security vendors, you have one team coordinating everything. They filter alerts, investigate threats, and only escalate what actually needs your attention.
Best for: Small to medium businesses that lack dedicated security staff or organizations tired of vendor management complexity.
2. Advanced Alert Filtering and False Positive Elimination
Modern managed security services use machine learning to distinguish between real threats and system noise. This isn't just basic filtering: it's intelligent prioritization based on your specific environment and business patterns.
What this eliminates: Those 3 AM alerts about routine system updates. Notifications about "suspicious" activity that's actually your night shift accessing normal files. Duplicate alerts from multiple systems detecting the same non-issue.
The result: Your team sees 60-80% fewer alerts, but catches 95% more actual threats.
3. Managed Detection and Response (MDR)
MDR combines advanced threat detection with human expertise to investigate and respond to security incidents. Unlike basic monitoring, MDR teams actively hunt for threats and take immediate action when they find them.
How it reduces fatigue: Instead of your team analyzing every endpoint alert, MDR specialists investigate first and provide context. You get executive summaries like "WordPress plugin vulnerability exploited on web server, threat contained, patch applied" instead of 47 individual system alerts.
Perfect for: Organizations that need enterprise-level security without building an internal SOC.
4. Platform Consolidation and Tool Integration
The average enterprise uses 35 security vendors with 70+ individual products. Consolidation brings these tools under unified dashboards and coordinated workflows.
Why this matters: When security tools can't talk to each other, they each send their own alerts about the same incident. Consolidation means one alert, one investigation, one response: not five separate fire drills.
Implementation tip: Start by consolidating tools from the same vendor family, then gradually integrate third-party solutions that offer robust APIs.
5. SIEM/SOAR Integration
Security Information and Event Management (SIEM) collects data from all your security tools. Security Orchestration, Automation, and Response (SOAR) automates responses to common threats.
The magic happens when: SOAR automatically handles routine incidents (like blocking known bad IP addresses) while SIEM escalates only complex threats requiring human analysis.
Real-world impact: One client reduced their daily alert volume from 2,000+ to fewer than 50 actionable items using properly configured SIEM/SOAR integration.
6. Centralized Identity and Access Management
When employees struggle with multiple passwords and authentication systems, they create security workarounds. Centralized identity management reduces both security gaps and alert volume.
Alert reduction: Fewer failed login attempts, reduced account lockouts, and streamlined access reviews mean fewer security notifications flooding your inbox.
User experience bonus: Your team spends less time managing access requests and more time focusing on real security issues.

7. Policy-Driven Security Fabric
Automated policy enforcement reduces configuration errors and ensures consistent security across your entire infrastructure. When security policies are embedded in your architecture, compliance becomes automatic.
How it cuts alerts: Automated compliance monitoring eliminates most manual auditing alerts. Policy violations are prevented before they happen, not detected after the fact.
Scalability factor: As your business grows, policy-driven security scales without proportionally increasing your alert volume.
Frequently Asked Questions
Q: Will managed security solutions work for smaller businesses?
Absolutely. Smaller businesses often benefit most because they typically lack dedicated security staff. Managed solutions provide enterprise-level protection without enterprise-level complexity or costs.
Q: How quickly can we see alert reduction?
Most organizations see 40-60% alert reduction within the first 30 days of implementation. Full optimization usually takes 60-90 days as systems learn your environment and fine-tune filtering rules.
Q: What about compliance requirements?
Managed security solutions often improve compliance by providing better documentation, automated reporting, and consistent policy enforcement. Many solutions include compliance management as part of their service.
Q: Can we maintain some internal security control?
Yes. Most managed security models offer hybrid approaches where you retain control over critical decisions while outsourcing routine monitoring and response activities.
Q: How do we measure success beyond alert reduction?
Look at incident response times, false positive rates, staff satisfaction, and time-to-detection for actual threats. The best solutions improve all these metrics simultaneously.

Implementation Strategy
Start with one consolidated solution rather than trying to fix everything at once. Many organizations begin with MDR services to immediately reduce alert fatigue, then gradually add other managed services as they see results.
Key success factors:
- Clearly define what constitutes a "high-priority" alert for your business
- Ensure managed service providers understand your industry and compliance requirements
- Establish regular review cycles to optimize filtering rules and response procedures
- Train your remaining internal team on how to work effectively with managed services
The goal isn't to eliminate all security alerts: it's to ensure that every alert your team sees actually needs human attention.
Stop Fighting Alert Overload
Cybersecurity fatigue is a business risk, not just an IT inconvenience. When security teams are overwhelmed, real threats get missed. When tools don't work together, gaps appear in your defenses.
Premier Business Team helps Pacific Northwest businesses implement managed security solutions that reduce alert noise while strengthening protection. We've seen organizations cut their daily alert volume by 75% while improving their actual security posture.
Ready to give your security team some breathing room? Call us at 360-946-2626 to discuss which managed security solutions make sense for your specific environment. Let's turn your security tools from a source of stress into a competitive advantage.

