Here's the reality for most growing businesses: You've got momentum. Sales are climbing. Your team is expanding. Everything looks great on paper.
But behind the scenes? Your IT infrastructure is quietly becoming a bottleneck. Server costs are climbing faster than your revenue. You're calling support and waiting hours for callbacks. Your team is complaining about slow systems. And you're stuck in a cycle where scaling your business means scaling your IT problems right alongside it.
Sound familiar? You're not alone: and there's a better way forward.
What Is Infrastructure as a Service (IaaS)?
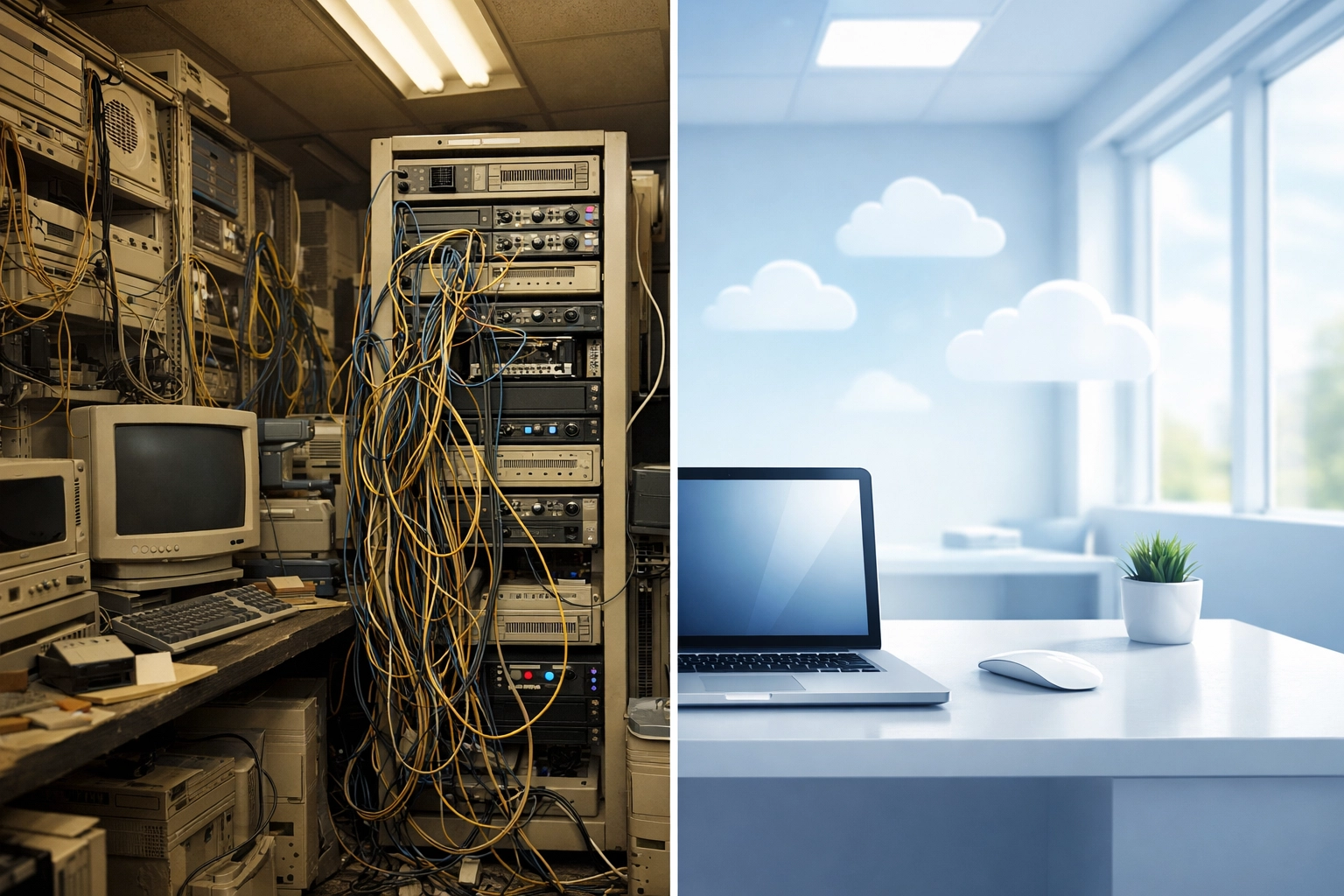
Infrastructure as a Service (IaaS) is a cloud computing model that delivers the foundational IT resources your business needs: servers, storage, networking, and virtualization: without the hardware headaches.
Instead of buying physical servers, maintaining server rooms, paying for cooling systems, and employing full-time staff to keep everything running, you access enterprise-grade infrastructure on demand. You pay only for what you use, scale up or down as needed, and let a managed cloud provider handle the heavy lifting.
Think of it like leasing office space instead of buying a building. You get everything you need to operate effectively, but without the massive upfront investment, ongoing maintenance costs, or long-term commitment to outdated equipment.

The Problem: Growth Shouldn't Feel Like a Penalty
Most businesses don't set out to create infrastructure problems. The issues creep up gradually as you grow:
Rising IT Costs That Don't Match Your Growth
You added 15 employees last year, but your IT costs went up 40%. You're paying for server capacity you don't use most of the time "just in case" you need it during peak season. Hardware refresh cycles hit your budget like clockwork, and every upgrade feels more expensive than the last.
Limited Visibility Into What's Actually Happening
When something goes wrong, you're flying blind. Is it a network issue? A server problem? A storage bottleneck? You're piecing together information from multiple vendors and hoping your internal IT person can figure it out before the business is impacted. (If you want a clearer framework for modern WAN infrastructure, see our guide: What is SD-WAN? A Business Guide.)
Slow Support That Can't Keep Up
You submit a ticket and wait. Then you follow up. Then you wait some more. Meanwhile, your team is sitting idle, customers are getting frustrated, and you're losing productivity: and revenue: by the hour.
Scaling Feels Impossible Without Major Investment
Opening a new location? Rolling out a new application? Expanding your team? Every growth move requires months of planning, major capital expenditure, and infrastructure projects that pull your IT resources away from strategic work.
The worst part? You know your competitors aren't dealing with this. They're moving faster, spending less, and somehow their systems just… work.
The Solution: Managed IaaS Built for Real Business Needs
A properly deployed Infrastructure as a Service platform eliminates the traditional tradeoffs between cost, performance, and scalability.
Flexibility Without Complexity
IaaS gives you access to enterprise-grade infrastructure that adapts to your business. Need more storage next month? Done. Expanding into a new region? Spin up resources in minutes, not months. Testing a new application? Deploy it without buying new hardware or reconfiguring your entire network.
The infrastructure scales with you: not ahead of you or behind you.
Performance You Can Actually Feel
Managed IaaS providers operate geographically distributed data centers with redundancy built into every layer. That means faster load times, better responsiveness, and systems that stay online even when individual components fail.
Your team notices the difference immediately. Applications respond faster. File transfers complete quicker. Video calls don't freeze during important meetings. It's the kind of performance you'd expect from a Fortune 500 company: because you're running on the same infrastructure they use.
Compliance and Security Built In
Data breaches, compliance violations, and security gaps keep business owners up at night. With managed IaaS, you get automatic data backups, multi-factor authentication, encryption, disaster recovery, and compliance frameworks built into the platform. (For a deeper look at how to approach security program-wide, read: Cybersecurity Risk Management.)
You're not adding security as an afterthought. It's baked into every layer of the infrastructure from day one.
The Outcomes: Real Results for Growing Businesses
When businesses switch from traditional on-premises infrastructure to managed IaaS, the results are measurable and immediate:
50% Reduction in IT Costs
Eliminate capital expenditures on servers, storage, and networking equipment. Cut costs associated with power consumption, cooling, server room space, and hardware maintenance contracts. Shift from unpredictable capital expenses to predictable monthly operating expenses that scale with your actual usage.
One of our clients was spending $18,000 monthly maintaining aging on-premises servers. After migrating to managed IaaS, their monthly costs dropped to $8,500: and their performance improved dramatically.
Faster Performance and Better Responsiveness
Access to enterprise-grade infrastructure means your applications run faster, your team works more efficiently, and your customers have better experiences. No more "the system is slow today" complaints. No more productivity losses waiting for files to load or applications to respond.
Simplified Scaling Without Adding IT Resources
Open new locations, onboard new employees, launch new applications, and expand into new markets without hiring additional IT staff or making major infrastructure investments. Your IaaS platform grows with you automatically.

How IaaS Works in Practice
Let's look at a real-world scenario:
You're a growing professional services firm with 75 employees across three offices. You're planning to open two more locations next year and add 30 new team members.
Traditional Approach:
- Budget $125,000 for new servers and networking equipment
- Spend 3-4 months on procurement and installation
- Hire an additional IT person to manage the expanded infrastructure
- Cross your fingers that you estimated capacity needs correctly
IaaS Approach:
- Provision resources for new locations in under an hour
- Add users and applications as needed with a few clicks
- Pay only for what you actually use as you grow
- Let your managed IaaS provider handle infrastructure management while your IT team focuses on supporting your business strategy
The difference isn't just cost: it's speed, flexibility, and the ability to focus on growing your business instead of managing infrastructure.
When to Consider IaaS for Your Business
Infrastructure as a Service makes sense when:
- You're experiencing rapid growth and your current infrastructure can't keep up
- IT costs are rising faster than your revenue
- You're opening new locations or supporting remote/hybrid teams
- Your internal IT team is overwhelmed with maintenance and support
- You need enterprise-grade security and compliance but don't have the internal expertise
- Hardware refresh cycles are draining your capital budget
- You want to focus internal resources on strategic initiatives instead of infrastructure management
If you're dealing with any combination of these challenges, it's time to explore how managed IaaS can transform your IT infrastructure from a cost center into a competitive advantage.
Frequently Asked Questions About IaaS
How quickly can we migrate to IaaS?
Most businesses complete their IaaS migration in 30-90 days depending on complexity. Simple migrations with standard applications can happen faster. The process includes assessment, planning, migration, testing, and optimization: and your managed provider handles the technical heavy lifting.
What happens to our data during migration?
Your data is securely transferred to the cloud infrastructure with encryption in transit and at rest. Managed IaaS providers follow strict protocols to ensure zero data loss and minimal downtime during migration. Most migrations happen in phases to reduce business disruption.
Can we integrate IaaS with our existing applications?
Yes. Modern IaaS platforms are designed to work with existing business applications, whether they're commercial software, custom applications, or legacy systems. Your provider will assess compatibility during the planning phase and design the infrastructure to support your specific application requirements.
How does IaaS pricing actually work?
IaaS pricing is typically consumption-based. You pay for compute resources (processing power), storage capacity, data transfer, and any additional services you use. Most providers offer transparent monthly billing with detailed usage reports, making it easy to track costs and optimize spending.
What about disaster recovery and business continuity?
Managed IaaS platforms include built-in disaster recovery with automated backups, geographic redundancy, and rapid recovery capabilities. If something goes wrong, you can restore systems quickly without managing complex backup infrastructure yourself.
Transform Your IT Infrastructure Today
If rising IT costs, limited visibility, and slow support are holding your business back, it's time to explore what Infrastructure as a Service can do for you.
Premier Business Team specializes in deploying managed IaaS solutions designed specifically for growing businesses. We handle the technical complexity, you enjoy the benefits: lower costs, better performance, and the flexibility to scale without infrastructure limitations.
Ready to cut your IT costs in half while improving performance? Contact Premier Business Team today to schedule a free infrastructure assessment and discover how IaaS can accelerate your business growth.